Blog — Data Recovery and Cybersecurity
Technical analyses, prevention tips and data recovery news from the experts at SOS Data Recovery, Swiss laboratory since 2006.
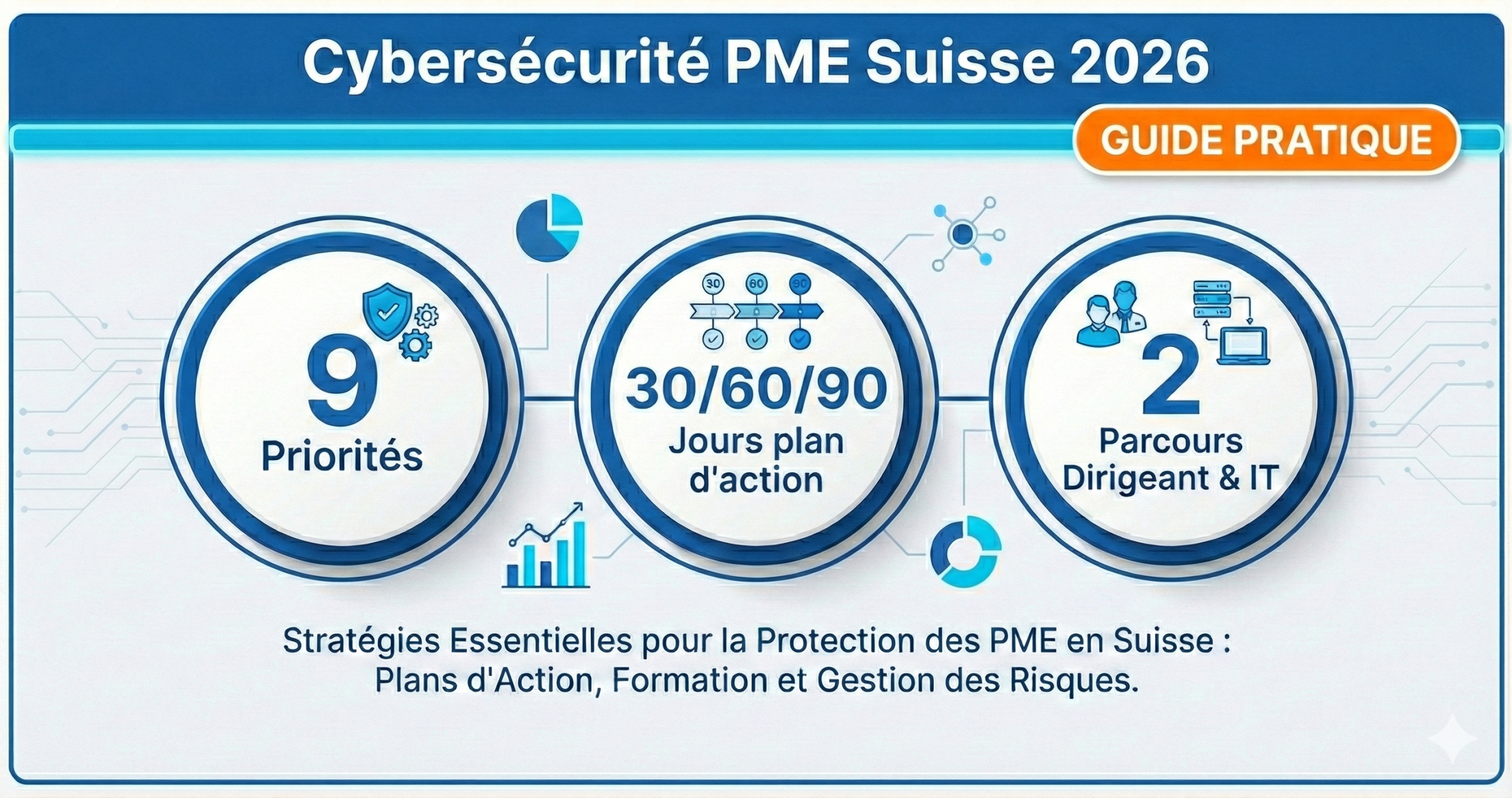
Swiss SME Cybersecurity: 2025 Summary & 30/60/90-Day Action Plan for 2026
In 2025, a reality has become clear: most incidents do not come from a spectacular "hack," but from a chain of avoidable failures: reused password, weak authentication, overly broad permissions, delayed updates, untested backup... and a phishing email that gets through.
The objective of this article is to give you a clear, actionable, and prioritized summary for SMEs with 10–50 and 50–250 employees, with two reading paths:
• Manager / executive (simple decisions with high ROI)
• IT / service provider (concrete implementation)
Manager or IT: choose your reading
Want the essentials without the jargon? Read the Manager Version.
Want the implementation details? Switch to the IT Version.
Manager Version (priorities)
IT Version (checklists)
The 9 priorities for 2026 (express summary)
- Enable MFA (Multi-Factor Authentication) on critical accounts (email, cloud, VPN, admin)
- Stop password reuse (and adopt a password manager)
- Reduce access rights (principle of least privilege)
- Implement updates as a “system” (policy + automation)
- Monitor vulnerabilities (monitoring + prioritization)
- Strengthen anti-phishing reflexes (short and regular training)
- Structure backups (and test restoration)
- Prepare for crisis management (Cyber Action Plan: roles + checklists)
- Adopt a Zero-Trust approach (progressive, pragmatic)
Part 1 — Managers / Executives: secure without becoming an expert
If you are a manager, executive, or responsible for admin/finance or operations: this section gives you a simple plan with high ROI (without jargon) to reduce risk in 30 days.
1) The fastest ROI: protect access (MFA + passwords)
MFA: if you only do one thing this month, do this. MFA strengthens access to emails, the cloud, business tools, and administrator accounts.
Read: MFA for Swiss SMEs — 2025 guide
Passwords: an "OK" password that is reused becomes a "dangerous" password. Aim for: passphrases, password manager, and a simple rule: one service = one unique password.
Read: Strong Password — 2025 guide
Expected result: fewer account takeovers, fewer incidents that start "through email".
2) Reduce the impact of an incident: the principle of least privilege
Even with good protections, an account can be compromised. The difference between a "manageable" incident and a crisis often comes down to a single question: what exactly was this account allowed to do?
"Each person only has the necessary access. No more, no less."
Read: Principle of Least Privilege — 2025 guide
Expected result: a compromised account does not allow an attacker to "traverse" the entire company.
3) Updates & vulnerabilities: the hygiene that avoids disasters
Known vulnerabilities are exploited... because they remain unpatched. Two complementary levers:
- make updates a routine (policy, maximum deadlines, automation),
- monitor vulnerabilities to prioritize correctly.
2025 Resources:
To illustrate the issue, you can also consult an example of monthly statistics (2025):
Expected result: fewer opportunistic attacks, fewer "open doors".
4) Business continuity: backups (and restoration test)
An untested backup is not a strategy: it's hope. Your vital minimum:
- automated backups,
- redundant copies,
- planned restoration test,
- priority to business data (customers, finance, production, HR).
Read: Backup Security Plan — 2025
Expected result: faster business recovery, lower stress, clearer decisions.
5) The day of: have a crisis plan (Cyber Action Plan) ready
The question is no longer "if" but "when". A Cyber Action Plan (CAP) avoids improvisation at the worst moment.
To plan for:
- roles & responsibilities (management / IT / service provider / communication),
- scenarios (email compromise, ransomware, data leak),
- decision checklists (isolate, communicate, restore).
Read: Cyber Crisis Management — CAP (2025)
Expected result: faster reaction, limited impact, controlled communication.
30 / 60 / 90-day action plan (management version)
-
0–30 days: immediate risk reduction
-
MFA enabled on critical accounts
-
"unique passwords" rule + recommended password manager
-
1 backup restoration test
-
phishing quiz shared with the team
31–60 days: structuring
-
least privilege (admin rights reviewed, "overly broad" access removed)
-
update policy (max deadlines + automation)
-
vulnerability monitoring / prioritization routine
61–90 days: maturity
-
Cyber Action Plan version 1 + short exercise
-
phishing training on a regular schedule (micro-format, regular)
-
first steps Zero-Trust (progressive)
-
Manager or IT: choose your next step
Manager: the 30/60/90-day roadmap above is enough to get started.
IT / service provider: continue for implementation (checklists).
Go to the IT version
Return to the beginning of the Manager version
Part 2 — IT / Service Providers: the implementation checklist (without unnecessary complexity)
Objective: transform the above priorities into concrete deployment, with clear tasks and a pragmatic approach (SME 10–50 / 50–250).
A) Identities & Access (IAM) — order of battle
- Inventory of accounts (admins, shared mailboxes, service providers, dormant accounts)
- MFA everywhere possible (email, cloud, VPN, admin)
- Hardening: limit admins, quarterly review of rights, deletion of unnecessary access (least privilege)
2025 Resources:
B) Patching & vulnerabilities — make security "regular"
- patching policy (max deadlines per criticality)
- automation as soon as possible
- vulnerability monitoring → prioritization → execution → proof (update log)
2025 Resources:
C) Mobility & BYOD — secure without hindering productivity
Two real-world realities for SMEs: teams move around, and personal devices are (sometimes) used for work. The idea is not to prohibit: it is to frame with simple rules.
To standardize:
- prioritize 4G/5G sharing rather than public WiFi
- VPN (or equivalent solution) to encrypt connections
- no access to critical services on unverified networks
- BYOD policy: locking, updates, separation of professional/personal, storage rules
2025 Resources:
D) Phishing: train + measure + anchor
Effective awareness is short, regular, positive, and measurable. Phishing is best combatted with reflexes than with rules "on paper".
To delve deeper (2025):
- Phishing in business: how to recognize and counter (SME)
- PhishTrainer: new phishing simulation tool (Switzerland)
Immediate action (10 min): get a clear starting point with the phishing quiz.
Take the phishing quiz (10 min)Discover PhishTrainer
E) Backups & recovery — moving from "backup" to "recovery"
Minimum checklist:
- define RPO/RTO (acceptable data loss / acceptable downtime)
- automated backups + isolated copies when possible
- planned restoration test + simple procedure "restore in crisis"
F) Sensitive data: when to add a "premium" layer
For certain documents (customers, HR, finance), client-side encryption provides useful additional protection, especially in a cloud context.
Read: Client-Side Encryption — 2025
G) Zero-Trust: a progressive logic (SME-friendly)
Pragmatic Zero-Trust version: verify, segment progressively, reduce lateral movements, strengthen authentication.
SME 10–50 vs 50–250: adapt without overloading
If you are 10–50
- aim for simplicity: MFA + manager + auto updates + tested backups
- 1 internal contact + an external partner if necessary
- culture: 1 rule = 1 reflex (not 20 pages of policy)
If you are 50–250
- aim for repeatability: piloted patching, access by roles, regular reviews
- industrialize onboarding/offboarding (access, equipment, procedures)
- governance: 30 minutes "cyber" per month in the management committee
Conclusion: your next (simple and measurable) step
Want to move from "we know" to "we do"?
- Start with the phishing quiz (10 minutes):
https://academy.bexxo.ch/fr/formation/quiz/quiz-reconnaitre-signaux-phishing-ingenierie-sociale.html
- Apply the 30/60/90-day plan: access (MFA + passwords), rights (least privilege), updates + monitoring, tested backups, Cyber Action Plan, and training schedule.
To understand why SMEs are particularly exposed (2025):
Cybersecurity: why are SMEs particularly vulnerable?
2025 Readings cited (references)
- Vulnerable SMEs: why? (March 19, 2025)
- Crisis Management: Cyber Action Plan (March 28, 2025)
- PhishTrainer: phishing simulation (May 22, 2025)
- CVE Statistics — June 2025 (July 2, 2025)
- Public WiFi on the go (August 20, 2025)
- Backup Security Plan (August 15, 2025)
- Zero-Trust (September 23, 2025)
- Password Guide (September 10, 2025)
- MFA (October 8, 2025)
- Client-Side Encryption (November 24, 2025)
- Least Privilege (November 4, 2025)
- BYOD (December 4, 2025)
- Updates & Vulnerabilities (2025)
- Monitor Vulnerabilities (CVEFind) (2025)
- Phishing in Business (SME) (2025)

